Mobile Security for Pharma:
protecting most valuable assets.
Pushed by regulators and a strategic and vital need for Intellectual property protection, The pharmaceutical industry has always excelled in applying strong and cutting edge security measures.
As for other sectors, Pharma needs to implement digital transformation and extend the use of mobile devices and apps in order to give their teams more agility and effectiveness and offer a better service to their customers. Hence, Mobile Security must now be a new focus, as Drug companies must protect sensitive patient data, cutting edge R&D information and IP, or their production process. Mobile devices are a new threat vector cybercriminals and industrial spy are using to try and access this sensitive information and Intelectual Property.
Smart and efficient mobile threat defense posture is of vital importance to protect most valuables assets of Pharma Business against cyberattacks and information leaks.

Protecting employee devices
Researchers, executives and business reps of pharma companies are increasingly relying on mobile devices for both work and personal use, and employees may be accessing company data outside the office to stay productive. Even if corporate IT tries to lock down device usage, security in a world of connected smartphones, tablets and IoT devices, in labs and in the field, cannot be entirely assured by conventional methods.
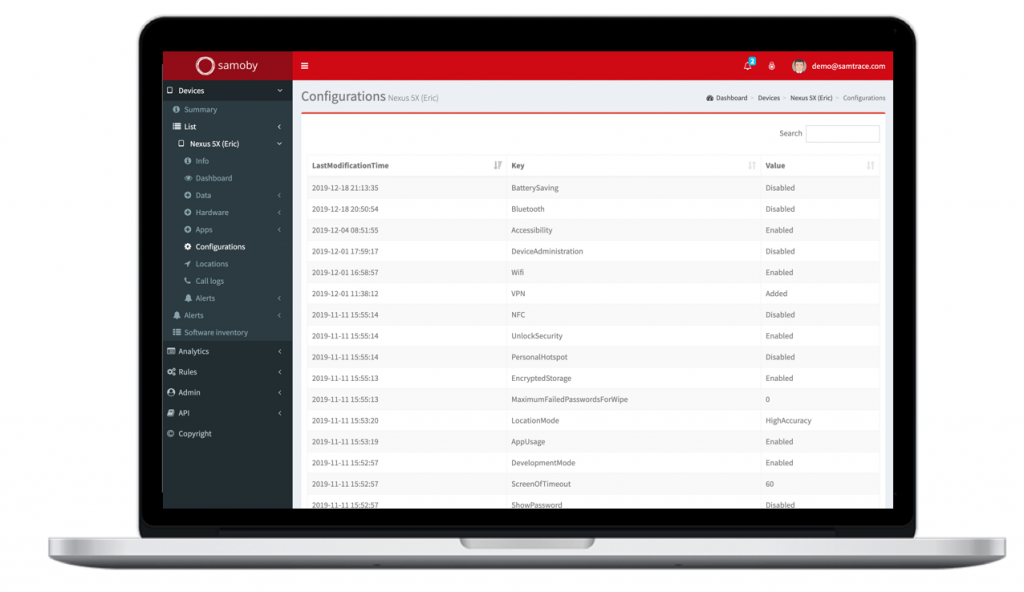
Security Regulations requires us to monitor as much as possible employee devices to detect potential leaks and attacks, while privacy regulation prevent us from lurking within this data.
Whether using company or personal devices (BYOD), Employees tend not to be aware of the risks they are exposed to, and tend not to apply basic precautions such as keeping their devices updated, avoid connecting to unknown Wi-Fi networks, clicking on an unknown link or site or download potential malware apps. Although Google and Apple build in some security features, new vulnerabilities are discovered every day, and new security updates are published constantly.
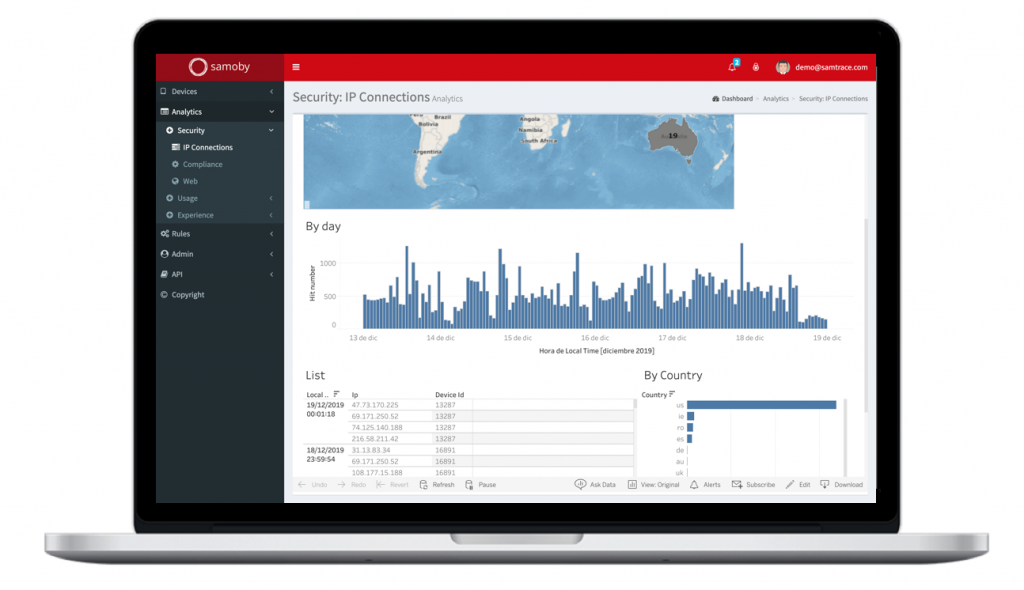
Rogue networks
Applying strict security policies over company’s corporate and R&D networks may not be enough if an attacker tries to induce you to connect to a rogue network making you believe you are connected to a known one. Even without noticing it, your device might connect automatically to a fake “Free Wi-Fi” access point because that network was saved as a known network in your device. The attacker that control that network will then be able to act as a Man-in-the-Middle (MITM) and intercept your private data communications, or even connect to your device and operate them remotely.
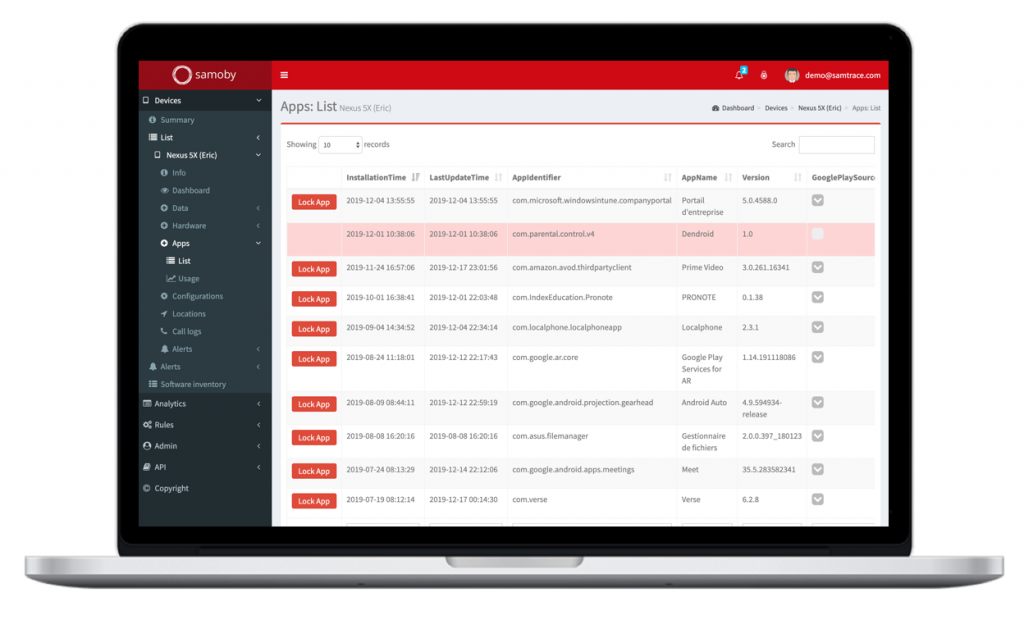
App Protection
Pharma companies are developing mobile apps for their patients and physicians, in order to give them the best possible service, increase prescription adherence, avoid interactions, or get real time information and measures during clinical trials. As they are dealing with highly sensitive health information, these apps and the devices they are running on must have the best possible protection.